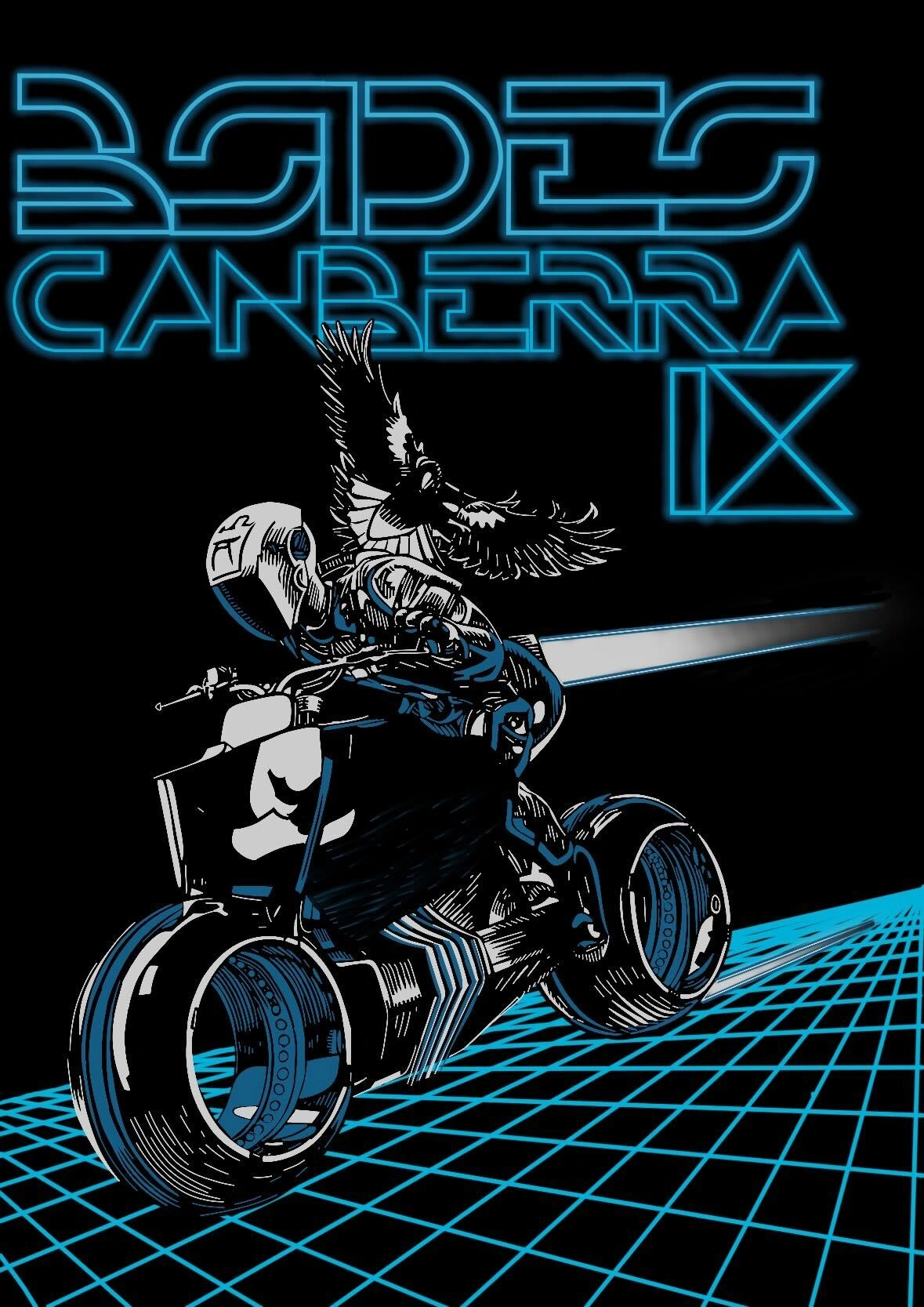
CSides Canberra
A free, monthly technical meetup for the local cyber community. Two talks, good chats, and a friendly room.
How it works
- No tickets, no fees. Just show up.
- Typically two technical talks.
- Beginners welcome. Questions encouraged.
- Post-talk catch-up nearby for food and a drink.
Next meetup
Date: 8th May 2026
Time: 6:00 pm
Location: Canberra Rex Hotel, Room 6
Afterwards: Swan & King Bar, Level 5
Time: 6:00 pm
Location: Canberra Rex Hotel, Room 6
Afterwards: Swan & King Bar, Level 5
Lifetime issues derived from unsafe rust
Rust is the (not so) new language to join the likes of C and C++, a compiled language ideal for systems programming. One of the biggest claims for rust is being memory-safe - that if one stays inside safe rust, they should never encounter memory corruption or undefined behavior. But rust has an escape hatch - 'unsafe' - often used for things such as FFI or handling MMIO. Through unsafe, one can implement unsound behavior - that can potentially lead to the horrors of undefined behavior. This talk focuses particularly on lifetime issues, how they can lead to fun things like dangling pointers and use-after-frees, and how to write your unsafe code properly to avoid such headaches.Zac
Zac is a security researcher at infosect. He's best nerd-sniped by asking him about some mix of binary exploitation, fuzzers, rust, and operating systems.Want to present?
We love practical talks, war stories, and deep dives. If you have something you are building, breaking, defending, or learning, it probably fits.
Please contact [email protected] to submit a talk..
Upcoming Dates
- 12th June 2026 - AI planning by John, Internet of Agents by Isaac
Past Talks
Friday 10th April 2026
Submarine Cables & Cyberz
Submarine cables are responsible for getting almost all international traffic to and from the island nation of Australia, yet most people have probably never seen them or thought much about them. We’ll cover what these cables actually look like in your hand, to what it could look like if we lose a handful of these cables, through to the more unsettling possibility that the biggest threat isn't a physical cut at all. Beyond sharks and ship anchors, risks lie in the management network, the supply chain, and who actually owns and builds this infrastructure. No prior knowledge required. Just bring your curiosity about what's really holding the global internet — and modern business and perhaps social order — together.Jocelinn Kang
Jocelinn Kang is the founder and managing director of Nodalys, a boutique national security consultancy working across cyber security, geopolitical risk, and digital resilience. After a career in government ensuring the confidentiality of packets, she moved to a think tank to ensure the integrity of policy conversations by helping decision makers understand the strategic ‘so what’ behind technology developments. Now she wants to ensure the availability of digital connectivity, because as it turns out, the global-ness of the internet relies heavily on a physical medium that is inherently exposed.
Friday 13th March 2026
Sebucsert: ASD's Unsolved CTF Challenge
For three years sebucsert sat live each year on Pecan+ and was only solved last year. An encrypted document, how the document was encrypted and nothing more, where no player or organiser could work out the solve and with no solution.md provided, it was dead in the water. Following the conclusion of the ctf 2025 and hearing about how the challenge would be shelved we decided that we were going to face the challenge and solve it.Sam & Ben
Sam Leong does a variety of IT-related things, like sysadmin, shaders and informatics, with the primary philosophy of 'if it ain't done right, do it yourself' Ben Pye has great interests in various things cybersecurity and sword fighting but is often found in ctfs, writing scripts to privately exploit games or listening to Master Boot Record.
Friday 13th February 2026
How to implement and compromise physical-layer security
Physical-Layer Security (PLS, not to be confused with physical security) is about making clever use of noise on the electromagnetic channel to make the decoding of bits impossible for eavesdroppers but not for the legitimate receiver. In theory, this provides 100% secrecy: if bits can’t be captured, they can’t be leaked and decrypted. PLS is very hard to implement though. So, instead, encryption is now the default solution for securing data on the move. But with the rise of quantum computing and Software-Defined Networking (SDN) we need to revisit this problem. In this talk I will demonstrate that with SDN effective implementation of PLS has become feasible and can contribute to a quantum-proof multi-layer defence. I will also show how the difference between theory and practice leads to actual vulnerabilities in PLS.Frank den Hartog
I am currently the Cisco Research Chair in Critical Infrastructure at the University of Canberra, focussing on safeguarding critical infrastructure from cyber threats and disruptions, and doing many fun projects with students in the fields of ZTNA, Private 5G/6G, Digital Twins, Programmable Networks, and PLS. Many of you may know me from an earlier stint at UNSW Canberra at ADFA though, where I taught cyber security into undergrad and postgrad programs, providing students with their first 150 hours of their 10,000 hours journey into becoming a cyber expert. And some of you know may even know me as a proficient singer of classical music. But don’t you worry, I won’t sing today.Why are we all such weirdos?
The hacker community is a bit... feral. Not in a bad way (like in the way that a cat that learned to open doors is feral). We taught ourselves things nobody asked us to learn, broke things nobody asked us to break, and then told everyone about it for free. For decades, this worked. More than worked, it built the internet, broke the internet, and then helped fix it (now it's broken again). This talk traces the arc of hacker culture from its roots in academic curiosity and people in basements through to the modern infosec industry, and asks a simple question: why does a community that routinely reverse-engineers million-dollar software for fun collectively lose its temper when someone suggests we might need a professional licensing body? The answer, it turns out, lives in anthropology, specifically, in my opinion, in Eric Raymond's observation that the hacker world operates as a gift culture. In a gift culture, status isn't derived from what you accumulate but from what you give away. Knowledge shared freely. Tools built and released. Vulnerabilities disclosed (eventually). The entire economy of respect in our world runs on contribution, not credential. Professionalisation — with its gatekeeping, its fees, its continuing professional development points, and its implicit message that you need permission to do this isn't just a bureaucratic inconvenience. It's a fundamental challenge to the value system the community was built on. It says: your worth comes from a piece of paper, not from what you've shipped, broken, or taught someone in a conference hallway at 2am. This talk is a well-meaning opinion piece that might make some of us in the industry understand why we are the way we are. Sounds spicy? hopefully will be just a laugh. Don't get on LinkedIn right now and start to @ me, listen to the talk first. After all it's free.Remy Coll
Remy Coll is Director and Principal consultant at Redacted Information Security. He does boring things like IRAP assessments and system security governance, and exciting things like smashing together physical and online CTF challenges. Remy, along with his esteemed colleague Simon, started the current series of Black Bag competitions that have been running at BSides for the last three years, and other places in between. He often teaches and delivers online training, as well as gives less fun talks about like, security planning and strategy and stuff.
Friday 9th January 2026
Grub Bootloader bugs and framework
Collecting Grub is the bootloader most commonly used in Linux desktops and servers. A bug in grub can be used for either bypassing secure boot, or maintaining persistence across a reboot once root has been achieved. This talk looks at a variety of bugs found in grub. I'll also discuss a framework for disabling secure boot utilising the grub configuration language. This is made more difficult that typical programming idioms aren't supported in the configuration language. For example, arithmetic is not native to the language, which makes mining memory difficult and hinders programming constructs such as iteration. However, arithmetic can be achieved through the use of the configuration langauge when it implements regular expressions and text substitution.Dr Silvio Cesare
Dr Silvio Cesare is a founder and Director at InfoSect, a vulnerability research company. He has worked in technical roles and been involved in computer security for over 29 years. This period includes time in Silicon Valley in the USA, France, and Australia. He has worked commercially in both defensive and offensive roles within engineering. He was previously the Director for Education and Training at UNSW Canberra Cyber, ensuring quality content and delivery. In his early career, he was the lead architect and developer for the startup Qualys, now the industry standard in vulnerability management. He has a Ph.D. from Deakin University and has published in academia, having been cited over 1000 times on google scholar. He is a 4-time speaker and also a trainer at the international industry leading Black Hat conference. He has taken his University research through commercialisation and authored a book (Software Similarity and Classification, published by Springer).
Friday 14th November 2025
Against Imperva's wishes, I made 10000 kids
Collecting data from the game of Pokemon Go involves bulk creation of accounts. In order to combat bots and other abusers of the game, a cloud WAF is used to prevent mass account sign-ups. This talk outlines some cheap techniques that can be used to bypass anti-bot measures employed by Imperva and other similar security platforms.Aeriana Lawler (Shiny Skitty)
Aeriana Lawler (Shiny Skitty) is a Linux sysadmin who these days [unfortunately] works in cyber security auditing. In their spare time, Skitty likes to level the playing field in Pokemon Go by developing tools to annoy spoofers in the game.